As the world revolves ever more around technology, understanding what occurs behind the infamous hacking screens becomes not only a fascination but a necessity. Like the passion and clarity that Elon Musk and Neil deGrasse Tyson bring to their fields, we aim to demystify and reveal the realities of hacking screens. Today’s cybersecurity landscape is vast and intricate, requiring critical scrutiny beyond the silver screen’s portrayal.
The Reality Behind Hacking Screens: Are They Really That Fast?
Picture this: a hooded figure furiously types away, and within seconds, “Access Granted” flashes on the screen. Cinematic hacking scenes make it look like a thrill ride at crazy cart speeds, but let’s tap the brakes. Here’s the scoop: the real hacking process is often methodical and painstakingly slow. Sure, there are tools to speed up parts of the process, but the dramatization you see has little in common with the typical speed and methodology used by hackers.
Real-world hackers and cybersecurity experts chime in with the truth. One tells us, “The laborious reality involves a lot of research, testing, and patience.” In fact, preparing a sophisticated attack can take weeks, if not months, of planning and execution. The hacking screen in a real hacker’s den is littered with open source tools like Metasploit and Nmap, lines of code, and a lot of trial and error, far from the instantaneous hack-jobs displayed in cinema.
Screen Mirroring

$0.00
Introducing the all-new Screen Mirroring technology the ultimate solution for sharing your smartphone, tablet, or computer screen with any modern television or monitor seamlessly. With just a few simple steps, you can cast your device’s display wirelessly, allowing you to present documents, share videos, or even stream games without the need for cumbersome cables or adapters. Our cutting-edge software ensures a stable connection with low latency, so your videos will play smoothly and your presentations will be cue-mark perfect. Screen Mirroring supports a wide range of resolutions, making it perfect for both high-definition entertainment and crisp, clear professional presentations.
Crafted with user convenience in mind, Screen Mirroring doesn’t require any complex setup or technical knowledge. The intuitive interface can be navigated with ease, enabling users to start mirroring in moments, without delving through convoluted menus or enduring lengthy installation processes. Whether you are in the boardroom or the living room, just a tap on your device lets you share your content on the big screen for everyone to see. Plus, with robust security protocols, you can have peace of mind knowing that your connections are protected and your data is safe.
For those looking to bring a more collaborative dynamic to their work or home entertainment setup, Screen Mirroring stands out as an essential tool. It effortlessly caters to the needs of educators who want to share interactive content with the whole classroom, business professionals aiming to enhance meetings with digital content, and households looking to enjoy multimedia from their personal devices on a larger display. Our technology supports a multitude of formats, ensuring compatibility with nearly all of today’s digital content. Embrace the power of Screen Mirroring and transform your viewing and sharing experience with unparalleled ease and functionality.
Hollywood vs. Hackers: The Truth About Visual Interface Designs
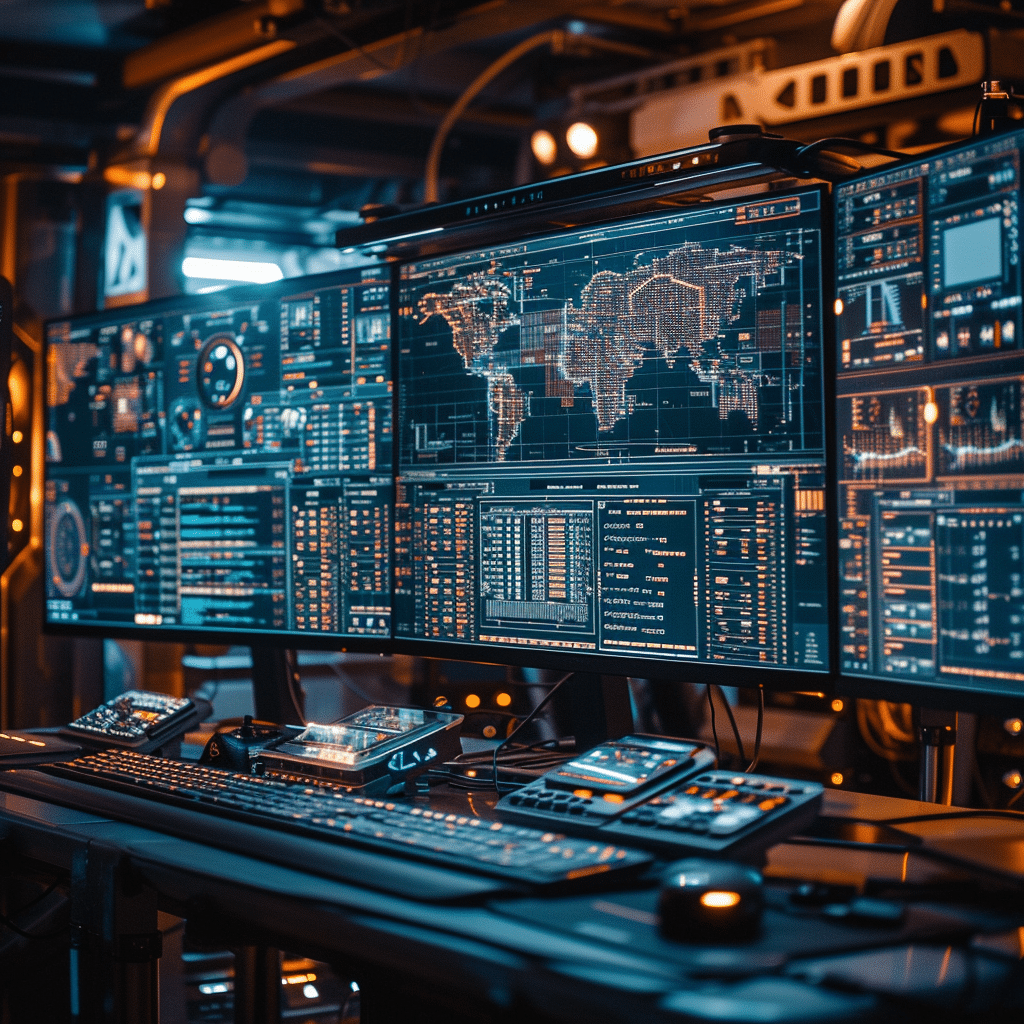
Gone are the days when the term “hacking screen” conjured images of green text on a black background, reminiscent of movies like “The Matrix.” Hollywood’s hacking visuals are all about theatrics—flashing windows, rotating 3D models, and rapid keyboard clatters. Let’s be real: actual hacking tools seldom come with the flashy user interface designs seen in “Swordfish.”
Cybersecurity experts and user interface (UI) designers opine that function overtakes form when it comes to hacker tools. “It’s about usability,” says one expert. “A compelling UI is good, but not at the expense of tool effectiveness.” The innards of bona fide hacks display plain, though sophisticated, command lines or text-based interfaces. They’re more about the Rizz—the efficiency—than the ‘wow’ factor.
| **Aspect** | **Details** |
|---|---|
| Definition | Hacking Screen: The act of gaining unauthorized access to a user’s device to capture or manipulate screen activity. |
| Common Methods | 1. Spyware/Malware Installation 2. Phishing Attacks 3. Remote Access Trojans (RATs) |
| Notable Hacker | *Kevin Mitnick* – Known as a prominent black-hat hacker turned ethical hacker. – Demonstrated significant hacking skills and social engineering techniques in his early years. |
| Access to Devices | Hackers can access: – Computer Cameras – Microphones – Screens All through the use of malware which allows remote control. |
| Risks & Consequences | – Unauthorized screen capture – Blackmail via recorded footage – Theft of credentials and sensitive data – Sale of stolen information on the dark web |
| Prevention Measures | – Use updated antivirus software – Regular system scans for spyware/malware – Caution when downloading apps and opening emails – Strengthening passwords and using multi-factor authentication |
| Potential Targets | – Individuals – Corporations – Government agencies |
| Impact on Victims | – Identity theft – Financial loss – Breach of privacy – Psychological stress due to blackmail |
| Legal Consequences | Legal actions against hackers may include: – Fines – Imprisonment – Seizure of equipment – Criminal records |
| Ethical Hacking | Ethical hackers like Kevin Mitnick use their skills to help secure systems. They conduct: – Penetration testing – Vulnerability assessments – Security audits |
| Data on Cybercrimes | – Growth in cybercrime related to webcam and microphone hacking – Increase in ransomware attacks involving screen access for blackmail – Spike in the sale of illegally acquired data on the dark web (as of Oct 25, 2023) |
The Art of Social Engineering: Bypassing Technology with Human Hacking
Social engineering is to hacking what hot Brunettes are to Hollywood—irresistible and often underestimated. This technique, which manipulates human psychology rather than assaulting digital defenses directly, has enabled many high-profile breaches. One of its patrons, Kevin Mitnick, a name that dazzles the world of hackers, turned his black-hat past into a force for good, unraveling the effectiveness of social engineering.
Mitnick’s explorations have demonstrated how a convincing phone call or a well-crafted email can be more potent than the most complex digital hacking screens. Recent exploits, like the Twitter Bitcoin scam, show how perpetrators need only a good story and a trusting victim to pull off a heist.
The Invisible Threat: How Hackers Hide Their Tracks on Screen
What if I told you that hackers are like ghosts? Almost—some can become nearly invisible. It’s not just about the hacking, but how they cover their tracks. One minute they’re on the hacking screen in all their glory, the next they’ve vanished into the digital ether. They use a variety of cloaking devices: think TOR for obfuscation, VPNs for disguise, and virtual machines for a clean getaway.
Ensuring absolute anonymity might involve booting into Tails OS or conducting activities through Whonix. These tools are like the invisibility cloak of the cyber world, hiding hackers’ movements from digital watchdogs.
Apulat Strong Neodymium Magnet; Used to Attach a Phone, a Tablet or a Second Screen to Your Laptop or Computer Monitor; Use The iPad as an Additional Display for Your MacBook;

$34.95
Introducing the Apulat Strong Neodymium Magnet: designed for modern professionals and tech enthusiasts seeking a seamless way to attach portable devices to their primary workstation. This sturdy magnet allows you to effortlessly affix a phone, tablet, or secondary screen to the side of your laptop or computer monitor, expanding your digital workspace with ease. Ideal for multitasking, the Apulat Strong Neodymium Magnet lets you use your iPad or another tablet as an additional display, perfect for extending the functionality of your MacBook or any other laptop. Its powerful magnetic grip ensures your devices stay securely in place, even during on-the-go use.
Crafted for versatility and convenience in any setting, the Apulat Strong Neodymium Magnet enhances productivity in a home office, co-working space, or while traveling. Whether you’re managing complex spreadsheets, engaging in video conferencing, or streaming media, this magnet provides a sturdy hold without the need for cumbersome clamps or stands. It’s incredibly user-friendly; simply attach the magnet to the back of your device and align it with your laptop or monitor you’re ready to work with an expanded, ergonomic view. Its slim profile ensures that it remains unobtrusive, maintaining the sleek aesthetic of your tech setup.
Not just for professionals, the magnet is a game-changer for anyone seeking a portable and robust solution to manage their digital landscape. The Apulat Strong Neodymium Magnet is powerful enough to support a range of devices, yet compact enough to carry in a laptop bag or backpack without adding bulk. Its compatibility with various tablets and phones allows for cross-device functionality, bridging the gap between your favorite gadgets. With the Apulat Strong Neodymium Magnet, you’ll redefine efficiency, turning any space into a dynamic, multi-screen environment at a moment’s notice.
Misconception of Complexity: The Simplicity of Some Hacks
The hacking screen can sometimes be a façade—there’s an assumption that every hack is a complex, cryptographic conundrum that challenges the highest intellects. While some attacks are undoubtedly complex, there’s elegance in simplicity. A surprisingly large number of successful cyberattacks are carried out using straightforward tools such as ‘phishing’ emails and ‘keyloggers’ that record keystrokes.
Phishing, for example, leverages the oldest trick in the book—deception. It’s less about technological prowess and more about delivering a convincing ruse.
The Portrayal of Instant Access: Debunking the Quick Entry Myth
Hacking screens in pop culture are like Jeon Yeo-been entering a scene—suddenly, everything’s happening, and objectives are achieved almost instantly. The truth? It’s like waiting for a new episode of eight Is enough—it takes patience. Stuxnet, for instance, an infamous piece of malware, was methodically deployed over a prolonged period to do its destructive work.
Real talk: getting through complex security systems typically involves numerous attempts and persistent efforts. Breaching could take minutes, sure, for lesser-protected systems, but it frequently takes much longer, especially for fortified networks.
Challenging the Typing Trope: Automation in Modern Hacking Procedures
Watching a hacking screen movie trope, you’d think all hackers are blazing-fast typists. But, let’s cut to the chase: automation is the word. Scripts and automated programs have usurped the ‘typing trope.’ Why thump away at the keyboard creating code when you can use PowerShell scripts or pre-packaged Metasploit payloads?
Nowadays, automation tools do the heavy lifting, and hackers focus on strategy and vulnerabilities. It’s like comparing the effort of walking to every house in the neighborhood to the efficiency of sending an electronic invite to a maya Hawke Movies And tv Shows marathon.
STREBITO Precision Screwdriver Set Piece Electronics Tool Kit with Bits Magnetic Screwdriver Set for Computer, Laptop, Cell Phone, PC, MacBook, iPhone, Nintendo Switch, PS, PS

$21.99
The STREBITO Precision Screwdriver Set is an indispensable toolkit designed for a wide array of electronic device repairs. This comprehensive kit includes various bits meticulously crafted to meet the precise requirements for fixing computers, laptops, cell phones, and gaming consoles such as the Nintendo Switch, PlayStation, and Xbox. Each bit is made from high-quality S2 steel, promising durability and a secure fit into tiny screws, ensuring you can tackle any repair job with confidence. The bits are magnetic, making it convenient to handle and place small screws, reducing the risk of losing them during disassembly.
Ergonomically designed, the kit’s screwdriver boasts a non-slip handle for a comfortable grip and optimal torque. The smooth swivel cap allows for continuous rotation, which is essential when removing or securing screws with precision and ease. Additionally, the screwdriver’s length and size enable it to reach recessed screws, making it possible to repair devices with more complex designs, like MacBooks or iPhones. Each tool in this kit is housed in a durable and portable case, keeping all components organized and ready for transportation.
The STREBITO Precision Screwdriver Set is more than just a set of tools; it’s a professional solution for tech enthusiasts, DIYers, and professional repair technicians alike. The thoughtfully selected range of bit sizes ensures you always have the right tool at hand for delicate electronics work. The case also features a clear layout, so selecting the right bit is straightforward and time-efficient. With its practical design and reliability, this tool kit allows you to extend the life of your electronics by making maintenance and repair both manageable and enjoyable.
Conclusion: Understanding the Hacking Screen Beyond the Silver Screen
By now, the veil is lifted on the hacking screen, revealing the stark difference between Hollywood’s fiction and the actual hacker world. This journey through the real and the embellished has shown us that understanding these truths is not just about separating fact from fiction—it’s about our security.
Educating the public on cybersecurity is crucial. Encouraging critical consumption of media representations of hacking can lead to a more savvy and secure online community. Remember, the next time you marvel at a hacking scene, there’s always more beneath the surface. Just as games like “it takes two” require partners to explore, understanding cybersecurity is a collaborative effort where knowledge is the gateway to protection.

In a world increasingly dominated by digital threats, being informed and vigilant is our best defense. Let’s take the knowledge we have unlocked today and use it as a shield against the invisible adversaries lurking behind the hacking screens.
The Truth Behind the Hacking Screen
Ever wondered if those flashy hacking screens in movies are just a bunch of hocus-pocus? Well, buckle up, because we’re about to dive deep and decode some of those mind-boggling hacking screen secrets that’ll leave your jaw hanging!
The Fictional Flair of Access Denied
Picture this: a hacker furiously types away as lines of code stream down the screen. Suddenly, a big red “ACCESS DENIED” flashes across. But hang on a sec! In real hacking scenarios, it’s not a Vegas marquee show. Usually, you’d get a bland, text-based prompt—way less dramatic, huh? The cinematic universe takes some serious creative liberties, making these scenes as riveting as a Hollywood blockbuster.
Decrypting the Gibberish
I bet you’ve seen a hacking scene where the screen is flooded with what seems like an ancient alien script. News flash: nine times out of ten, that’s a whole lotta gibberish. Actual hacking involves complex commands that an average Joe might find snooze-worthy. It’s not always a “hacker typhoon” blowing through the keyboard. More like a careful chess game, strategic and meticulous.
The Solo Act Myth
So you think a lone wolf hacker, fueled by pizza and the rush of breaking barriers, is the norm, right? Well, the life of a legit hacker is not a solo journey river green with admiration but often involves a team, each member with their own hacking prowess. Movies might love the “one genius against the world” trope, but in reality, collaboration is key, like the symbiotic gameplay in Games like it Takes two, where two heads (or more) are better than one.
The Hollywood Operating System
Ever noticed that eccentric, custom-designed hacking tools in movies? Here’s a fun fact: the real deal isn’t as “blinged out.” Real hacking doesn’t require a fancy “Hollywood Operating System” with 3D graphics and neon code. Legit hacking tools have user interfaces that might put you to sleep faster than counting binary sheep—simple, plain, but exceptionally powerful.
Time Warp Hack Attacks
Movies make it seem like hacking is as quick as snapping your fingers; in walks the hacker, types like a maniac, and bingo, they’re in! But hold your horses. In the real world, hacking can be a war of attrition, often taking days or even months of painstaking work. It’s not exactly the instant gratification spectacle that makes for edge-of-your-seat cinema.
Superhuman Typing Speeds
Ever chuckled at scenes where hackers go ham on the keyboard with the speed of a hyperactive squirrel? While fast typing can be handy, the accuracy and knowledge of the system you’re targeting are what truly count. So, unless you’re The Flash, let’s take those “keyboarding track star” scenes with a grain of salt, shall we?
Remember, the next time you see a hacking screen in movies, take it with a pinch of salt. Real hacking is less flashy and more about the nitty-gritty. So, don’t let Hollywood hack your perception of what truly goes on in the digital shadows. Keep it real and carry on learning the legit stuff!
Hacking WiFi Hacking, Wireless Hacking for Beginners step by step (How to Hack, Hacking for Dummies, Hacking for Beginners Book )
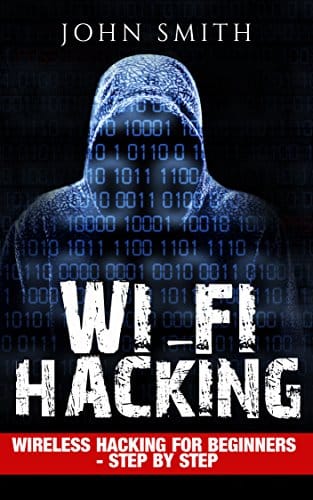
$3.49
“Hacking WiFi Hacking, Wireless Hacking for Beginners – step by step” is the ultimate guide for novices looking to penetrate the world of wireless security. Packed with clear, easy-to-follow instructions, this book demystifies the complex processes involved in compromising wireless networks. By focusing on practical steps and fundamental principles, readers are taken from basic concepts to executing successful hacks, all without overwhelming technical jargon. Whether for educational purposes or to understand potential vulnerabilities in your own network, this resource serves as a vital tool for any beginner.
To ensure a comprehensive understanding, “How to Hack, Hacking for Dummies, Hacking for Beginners Book” addresses the foundational aspects of cybersecurity and wireless protocols. Readers will learn about key topics such as WLAN infrastructure, encryption methods, and common vulnerabilities that hackers exploit. In addition, the book covers legal and ethical considerations of hacking, ensuring that readers understand the responsible use of the knowledge they gain. Each chapter builds upon the last, ensuring a smooth learning curve and a firm grasp of each hacking technique before moving on.
This practical guide doesn’t just stop at theory; it also includes real-world scenarios and step-by-step projects designed to solidify the readers skills. With hands-on exercises, readers are encouraged to practice in a controlled environment, allowing them to understand the repercussions of each action within the realm of wireless hacking. “Hacking WiFi Hacking, Wireless Hacking for Beginners – step by step” is therefore more than just a book; it is a complete beginner’s toolkit for understanding and implementing wireless security assessments, ensuring readers are equipped with the fundamentals necessary to start their journey into the world of hacking confidently.
Can hackers see your screen on your phone?
– Watch out! Hackers can definitely sneak a peek at your phone screen. They’re not using magic, though – it’s all about spyware or malware. These crafty apps wiggle their way into your mobile device, looking all innocent, but before you know it, they’re helping the bad guys capture your screen activity. Remember back on November 2, 2023? Yeah, that’s when we first got the scoop on this sneaky business.
Who is World No 1 hacker?
– Ah, Kevin Mitnick! This guy’s the Michael Jordan of hackers. Once a black-hat hacker causing digital mayhem, Mitnick has done a full 180, now wearing the white hat as an ethical hacker. Folks often say he’s the no 1 hacker in the world, and get this – his hacking high jinks kicked off way back in his early years!
Can a hacker see me through my computer screen?
– Sure as sugar, hackers can see you through your computer screen. Those cyber sneaks use malware like spyware to grab the reins of your camera, microphone, and yep, even your screen. I mean, it’s pretty wild (and creepy!) that they can just barge in and use those recordings to blackmail folks.
What do hackers do when they hack?
– Hackers, those digital ninjas, are all about getting their hands on the goods. We’re talking user credentials, secret data, and all that personal info you wouldn’t just hand to a stranger. Whether it’s phishing, malware, or smooth-talking their way past security, they snag this stuff and hawk it on the dark web for some shady shenanigans like faking IDs and raiding bank accounts.
What is the code to check if your phone is monitored?
– Dialing up a code to check if your phone is being watched? Now that would be handy, wouldn’t it? But, c’mon, wouldn’t life be a bit too easy if you could just punch in a few digits and – bam! – there’s your answer? Sadly, there’s no secret code that’ll spill the beans on whether your phone’s got unwanted company.
How do you know if your screen is being monitored?
– Feeling watched? Well, if your phone’s screen seems to be on the fritz, acting up, or if your battery’s running down faster than a kid down a water slide, these could be dead giveaways that someone’s monitoring your screen. Keep your eyes peeled for weird performance issues or out-of-nowhere apps and don’t shrug off those warning bells!
Do hackers have high IQ?
– High IQs and hackers? Well, not all brainiacs wear capes, right? It’s a no-brainer that some hackers might be rocking high IQ scores, but smarts alone don’t make the hacker. It’s a combo of mad skills, a knack for thinking outside the box, and, let’s face it, sometimes just plain being up to no good.
Who is the most feared hacker?
– When it comes to notorious hackers, there’s one that stands out from the pack. Think of them like the Big Bad Wolf of the digital world, so infamous that even other hackers might think twice before crossing paths. Although we might not drop names here, this cyber boogeyman’s reputation definitely precedes them.
Are hackers ever caught?
– Caught red-handed? Yep, hackers do get nabbed by the long arm of the law. It’s like hide and seek with high stakes. They might think they’re sly, covering their digital tracks, but make no mistake—many end up swapping their computer desks for a date with justice.
What are the 2 possible signs that you have been hacked?
– Two telltale signs of being hacked? Hold onto your hats: one, if it suddenly feels like your passwords just ups and walked away (because they’re changed without your say-so), and two, if your device suddenly becomes the life of the party (sending out oodles of spam emails or messages without you lifting a finger).
Can someone watch me through my TV?
– Prying eyes on your TV? Now that’s a scene straight out of a spy flick, right? While it’s technically possible for a smart TV to be hacked, unless you’re some bigshot or have seriously ticked off a hacker, chances are your TV watching is just between you and your couch.
Why do hackers ask for screenshots?
– Hackers asking for screenshots? Well, that’s as fishy as getting a soup sandwich. It looks like they’re on the hunt for some juicy info. Screenshots are like snapshots of your digital life—they can reveal what you’re up to, personal details, or even confidential business stuff.
What punishment do hackers get?
– Caught in the act, hackers face a whole menu of punishments. We’re talking fines that’ll make your wallet cry, or even some quality time behind bars. It’s a high-stakes game with consequences that are anything but a slap on the wrist.
What language do most hackers use?
– Hacker-speak isn’t just one language—it’s like their own Tower of Babel. But there’s a fan-favorite: Python. It’s easy to learn, incredibly versatile, and like a Swiss Army knife for coding. Other languages that get the hacker hearts racing include Java, C++, and the list goes on.
Should I delete my email if it was hacked?
– Hit the delete button on your hacked email? Whoa, hold your horses! Before you send your email address to the virtual graveyard, try reclaiming and securing it first. Change your passwords, update security questions, and check for any strange activity.
Can someone see my phone screen without permission?
– Sneaking a peek at your phone screen without a ‘please’ or ‘thank you’? That’s a no-fly zone, buddy. Without permission, it’s not just rude, it’s a downright invasion of privacy. So if someone’s doing it, they’re stepping way out of line.
Can you tell if someone is watching your phone screen?
– Got the jitters about someone watching your phone screen? It isn’t just a matter of paranoia. If your phone starts acting like it’s got a mind of its own or you spot strange apps doing a pop-up parade, somebody might be taking more than a casual glance your way.
Can someone watch me through my screen?
– Can someone watch you through your screen? If your digital fortress has been breached and malware’s taken up residence, then yep, it’s possible. Stay alert and keep your security software tight to avoid any peeping toms.
Can you see someone else’s phone screen on your phone?
– Seeing someone else’s phone screen on your own, without a bunch of tech wizardry? As much as that would give you a super-spy vibe, reality’s not there yet for the average Joe or Jane. Phones are personal business, and jumping into someone else’s without permission is a no-go.